


Every day, organisations worldwide face cyberattacks that range from phishing attempts to full-scale ransomware operations. Over 5600 ransomware incidents were publicly disclosed in 2024 alone, and US-based attacks surged 50% in the first ten months of 2025. Each breach carries a serious financial consequence – IBM’s 2024 Cost of a Data Breach Report puts the average cost of a single incident at $4.88 million. When a single event costs that much, the calibre of the people an organisation hires to defend against it becomes one of its most consequential decisions.
That figure is a global average, and it does not land the same way for every organisation. For small businesses, Verizon’s 2024 Data Breach Investigations Report puts the range at $120000 to $1.24 million per incident, and around 60% of those firms do not recover within six months. A breach is not a line-item expense – it reshapes how an organisation operates long after the incident is contained.
Yet preventing those breaches is harder than it looks. The ISC2 2024 Cybersecurity Workforce Study identified a global shortage of 4.8 million professionals, and organisations that operate with significant skills gaps pay on average $1.76 million more per breach than well-staffed peers. The roles at the centre of that gap demand more than technical knowledge – they require regulatory fluency, crisis-level judgment, and a degree of trust that general IT positions simply do not require. That combination is rare, and it is what makes cybersecurity hiring a discipline of its own.
Recruiters must identify candidates with niche certifications, hands-on experience, adaptability, strong communication skills, and demonstrated compliance awareness.
In this article, we explore the complexities of cybersecurity recruitment, highlight key industry trends for 2025, and explain how our specialized staffing process enables businesses to secure the right talent quickly.
Cybersecurity staffing is the targeted recruitment of experts who can protect digital assets, systems, and networks from evolving threats. Unlike general IT recruitment, cybersecurity staffing focuses on mission-critical roles – positions where a wrong hire can result in millions of dollars in losses, reputational damage, or regulatory penalties.

What sets cybersecurity staffing apart is its multi-dimensional complexity. It’s not solely about technical expertise – you’re also hiring for trustworthiness, crisis-readiness, and a deep understanding of regulatory frameworks. Many candidates hold industry-recognized certifications such as CISSP, CEH, or CompTIA Security+, which serve as indicators of both skill and credibility.
Equally important is their ability to communicate effectively across a wide range of stakeholders. Whether it’s collaborating with legal teams, HR, or executive leadership, cybersecurity professionals must translate technical risks into actionable insights for both technical and non-technical audiences.
How cybersecurity hiring differs from general IT recruitment
| Category | Cybersecurity expert | General IT developer |
|---|---|---|
| Skill sets and certifications | Specializing in threat detection, incident response, and penetration testing; requires certifications like CISSP, CEH, Security+. | Focus on infrastructure/app development; certifications like AWS, Azure, ITIL. |
| Role urgency and risk | High urgency; unfilled roles risk real-time breaches and penalties. | Moderate urgency; delays affect productivity but do not pose an immediate risk. |
| Adaptability to change | Must stay updated due to the rapidly evolving nature of threats. | Foundational skills remain relevant longer. |
| Impact of a poor hire | A poor hire can lead to breaches, legal issues, and financial loss. | A poor hire leads to inefficiency or project delays. |
| Talent availability | Severe shortage; high competition for skilled professionals. | More balanced supply-demand ratio. |
| Cross-functional communication | Frequently interacts with legal, HR, compliance, and executives. | Limited cross-department interaction. |
| Compliance knowledge | Deep knowledge of standards like GDPR, HIPAA, and PCI DSS. | Basic compliance awareness is not typically central to the role. |
The difference becomes clearer when you look at the specific roles organisations need to fill. Each one sits at a different point along the spectrum from hands-on technical work to executive-level strategy.
Industry-recognised certifications like CISSP, CEH, and CompTIA Security+ serve as baseline indicators of credibility, but they do not tell the full story. Trustworthiness and the ability to perform under pressure matter as much as any qualification, particularly for roles that touch sensitive systems or executive-level decisions. Cybersecurity professionals also need to communicate across organisational boundaries – translating technical risks into language that legal teams, HR, and executive leadership can act on.
As cybersecurity threats grow in complexity, so do organizations’ strategies to attract and retain top security talent.
2025 will bring new challenges and opportunities in cybersecurity staffing, shaped by shifts in technology, regulation, workforce preferences, and global demand.
Below are the most influential trends reshaping how companies approach cybersecurity recruitment today.
Generalist cybersecurity professionals remain critical – particularly for small and mid-size organisations where one person often needs to cover threat detection, incident response, and compliance at the same time. That role is arguably more demanding now than it was five years ago, precisely because the attack surface has expanded so quickly. At larger organisations, though, the growing complexity of modern threats is pushing hiring toward deeper specialisation. The areas seeing the sharpest increase in demand are:
For organisations at the stage where dedicated specialists make sense, these subfields represent where the most urgent hiring gaps exist. For those still building around generalist talent, understanding what each of these areas covers is equally important. It shapes what to look for when evaluating whether a candidate can handle the breadth the role demands.
Artificial intelligence and automation are increasingly used to improve recruitment efficiency. From sourcing to screening and scheduling, tools powered by AI now support:
While these tools accelerate hiring, they screen for what is observable: skills, certifications, and work history. What they cannot evaluate is whether a candidate can be trusted with access to an organisation’s most sensitive systems. Cybersecurity professionals sit at the centre of that trust: a wrong hire does not just slow a project down, it creates a potential threat from the inside. Human judgment at the final stage of the process is what closes that gap.
With top cybersecurity personnel frequently receiving numerous offers, firms are honing their employer brand by offering perks that go beyond standard tech benefits. In-demand professionals are attracted to firms that offer:
Retention is no longer a reactive process; it’s a strategic part of the recruitment cycle, especially in security-critical environments where high turnover carries significant operational risks.
These trends point to a future where cybersecurity staffing is more strategic, specialized, and proactive. Organizations that stay ahead of these developments and adjust their hiring practices accordingly will be better equipped to build high-performing, resilient security teams.
In today’s high-stakes digital environment, choosing the right cybersecurity recruitment partner can mean the difference between a fortified defense and a costly breach. The right agency helps you build resilient, regulation-ready security teams that can stop emerging threats and adapt to an ever-changing threat landscape.
“Cybercrime is the greatest threat to every company in the world.” – Ginni Rometty (former CEO of IBM, IBM Security Summit, 2015)
Here’s what to prioritize when evaluating potential partners:
Choose a partner with deep experience in roles like security analysts, threat intelligence experts, cloud security architects, and CISOs. Agencies that specialize in cybersecurity are better equipped to understand role-specific challenges and emerging threat models.
A strong resume does not prove that someone can perform under pressure. In cybersecurity, screening needs to go beyond standard interviews. The agency should put candidates through scenario-based evaluations – simulated breach responses where the candidate must detect, contain, and communicate a threat in real time. Penetration testing exercises test whether someone can think like an attacker, not just defend against one. Certification depth matters too: holding a CISSP or CEH is not enough if the candidate cannot demonstrate the reasoning behind it when pressed. For roles that carry access to sensitive systems, background and trust vetting should go beyond standard employment checks.
In sectors like finance, healthcare, or eCommerce, compliance is non-negotiable. Your agency should understand major frameworks (e.g., GDPR, HIPAA, PCI DSS) and deliver candidates who can maintain both security and compliance.
Great cybersecurity professionals are rarely on job boards. A strong partner should have access to:
Cybersecurity hiring rarely follows a predictable timeline. A post-breach recovery might require incident responders within days. An organisation scaling its SOC needs multiple analysts hired in parallel across different time zones. Others need executive-level security leadership without the overhead of a full-time CISO – a scenario where a virtual CISO engagement makes more sense. A good staffing partner recognises that each of these situations demands a different hiring structure and adjusts accordingly.
While cybersecurity staffing agencies offer speed, expertise, and access to niche talent, they’re not the perfect solution for every organization or scenario. Here are a few potential drawbacks to consider, along with strategies for mitigating them.
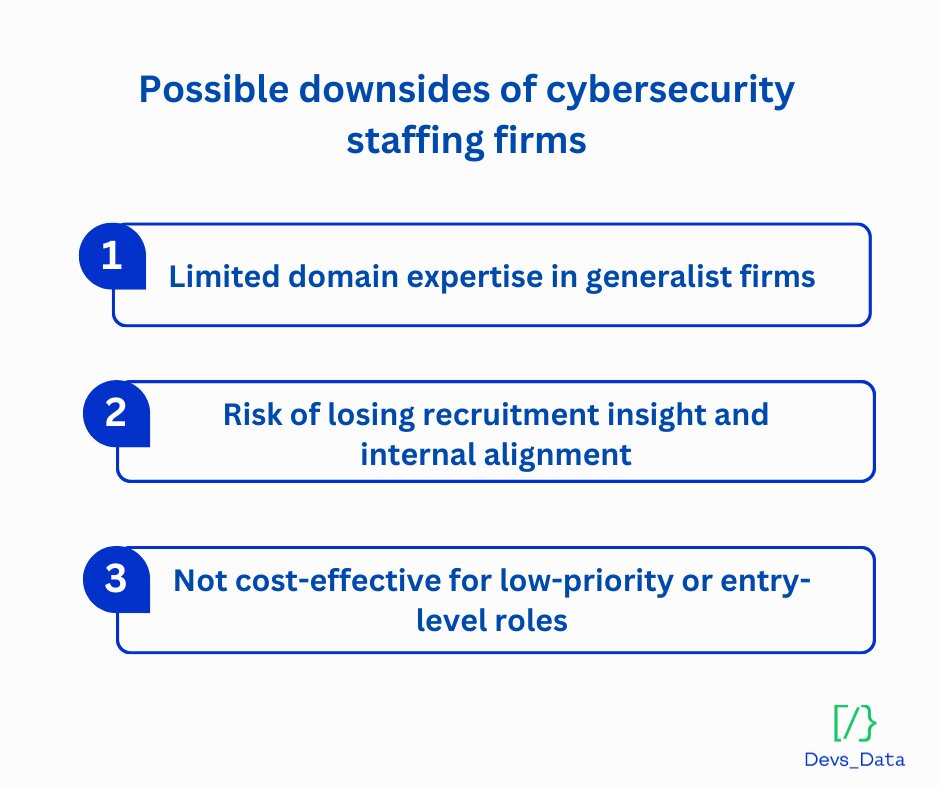
Not all agencies truly specialize in cybersecurity. Some general IT staffing firms may lack the technical depth or regulatory understanding needed to vet candidates effectively for high-stakes security roles.
What to avoid:
Overreliance on external partners can lead to a gradual loss of internal recruitment expertise and strategic alignment.
Overreliance on external partners can lead to a gradual loss of internal recruitment expertise and strategic alignment. When hiring decisions are outsourced too heavily, companies risk disconnecting from their own cultural fit criteria, long-term workforce planning, and evolving team dynamics. Additionally, agencies that rely on static candidate pools may miss out on emerging talent or passive candidates, limiting diversity and innovation in hiring.
When to be cautious:
How to stay in control:
Cybersecurity staffing services are most valuable for strategic hires, such as CISOs, SOC architects, and DevSecOps engineers, rather than for junior analysts or general IT roles.
When is it better to hire directly?
Cybersecurity professionals are among the most in-demand and costly hires in today’s global job market. Understanding the typical cost structure and the factors that affect pricing is essential for setting realistic budgets and making informed decisions.
When selecting a cybersecurity recruitment agency, having clear visibility into costs is just as crucial as ensuring technical expertise. It’s essential to collaborate with success-based partners like DevsData LLC, which only charges upon successful placement, thereby eliminating upfront risk and aligning incentives.
Transparent pricing is essential. Avoid agencies that add hidden fees for sourcing, screening, or onboarding, as these extras can quickly inflate costs and complicate your budgeting process. Look for flexible engagement models that support your specific hiring needs, whether contract, project-based, or full-time roles.
Finally, ensure the agency offers a guarantee period. A reputable partner will commit to replacing a candidate at no additional cost if the hire doesn’t meet expectations within a set timeframe, providing added peace of mind and reducing long-term hiring risk.
Agency fees are only one side of the budget. The candidate’s compensation varies significantly by role and location, and geographic sourcing is one of the most direct levers organisations have for managing costs. The table below shows current market rates across the US, Eastern Europe, and Latin America for the key cybersecurity positions covered earlier in this article.
Market rates by role (2025 estimates by Glassdoor)
| Role annual income | US | Eastern Europe | LATAM |
|---|---|---|---|
| SOC Analyst (Mid-Level) | $90,000–$120,000 | $40,000–$60,000 | $35,000–$55,000 |
| Penetration Tester | $100,000–$140,000 | $50,000–$80,000 | $45,000–$75,000 |
| Cloud Security Engineer | $130,000–$170,000 | $60,000–$100,000 | $55,000–$90,000 |
| CISO / Head of Cybersecurity | $180,000–$300,000 | $90,000–$160,000 | $80,000–$140,000 |
| DevSecOps / Security Architect | $120,000–$180,000 | $60,000–$110,000 | $55,000–$100,000 |
Note: Ranges depend on experience, certifications, engagement type, and risk level.
Several factors influence the cost of hiring in cybersecurity. Seniority and skill set play a significant role; specialized roles involving cloud infrastructure, AI/ML-based threat detection, or regulatory compliance (such as GDPR or HIPAA) typically command higher compensation. Geographic location is another key factor; hiring locally in high-cost regions such as the US or Switzerland can be significantly more expensive than sourcing talent from nearshore or offshore locations.
Security clearance also impacts pricing. Roles requiring background checks, government clearance, or access to highly sensitive data involve additional vetting and tend to offer higher salaries. Urgency of hire is another consideration – emergency placements or rapid team scale-ups following a breach may increase placement fees and necessitate premium compensation to attract top talent quickly.
One common mistake is underbudgeting for specialized roles. Positions such as CISO, cloud security engineers, or red teamers require competitive compensation, and failing to account for this can delay hiring or result in unsuccessful searches. Companies also often overlook the total cost of hiring, focusing solely on salary and ignoring additional expenses such as agency fees, onboarding, relocation, and time-to-productivity. These can significantly impact the overall budget.
Conversely, it’s also possible to overpay for lower-risk roles. Not every cybersecurity position requires a six-figure salary; entry-level SOC analysts or junior security roles can often be hired more cost-effectively, particularly when sourced from nearshore regions. A balanced, informed approach to budgeting is critical to avoid both overspending and costly delays.
There’s no universal formula for cybersecurity hiring. Threats are complex, the skill profiles are narrow, and the cost of a wrong hire is too high to treat recruitment as a generic process. As a cybersecurity-focused recruitment firm, DevsData LLC has spent nearly a decade building staffing models that account for exactly that complexity. Depending on what an organisation needs, whether it’s urgent incident coverage, long-term team building, or executive-level leadership, the right engagement structure will look different. The options below outline how we match each scenario to the appropriate model.
| Staffing service | When to choose | What makes it unique |
|---|---|---|
| Contract and project-based roles | For short-term needs, audits, or incident response without long-term commitment. | Quick onboarding; ideal for urgent or temporary risks (e.g., vCISO, penetration testers). |
| Full-time and permanent placements | When building in-house, long-term security teams with deep org knowledge. | Thorough vetting for cultural and technical fit; long-term organizational alignment. |
| Executive and leadership search | When cybersecurity leadership is needed to define strategy and manage enterprise risk. | Deep vetting with stakeholder input, emphasizing strategic and operational leadership. |
| Niche and emerging skill sets | When hiring for specialized roles in areas like cloud security, AI, or compliance. | Focus on hard-to-find skills; requires deep domain expertise beyond general IT hiring. |
| Custom recruitment solutions | When flexibility is required – e.g., hybrid teams, multi-location hiring, or high volume. | Tailored to business needs and structure, supports complex or sensitive hiring scenarios. |
These flexible options allow us to support everything from scaling a SOC team to filling one mission-critical role.
Website: www.devsdata.com
Company size: ~60 employees
Founding year: 2016
Headquarters: Brooklyn, NY, and Warsaw, Poland
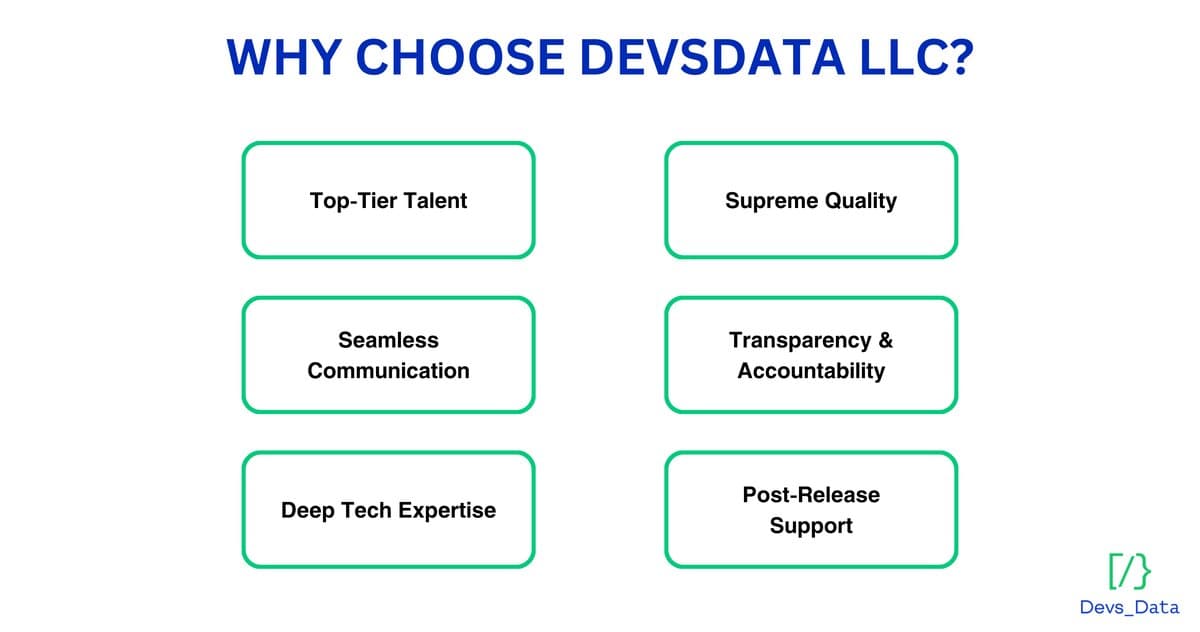
As a tech-focused recruitment firm operating globally since 2016, DevsData LLC brings deep cybersecurity domain knowledge and unmatched sourcing precision. We’ve helped both startups and global enterprises secure the right talent for their most sensitive roles.
We’re known for:
But what really makes our work effective is how we recruit – fast, focused, and tailored to the realities of cybersecurity hiring.
We operate on a success-fee model, which means you pay only when we deliver the right candidate, and we offer a guarantee period to ensure long-term satisfaction. Our track record speaks for itself: DevsData LLC holds a 100% client satisfaction rating on Clutch and GoodFirms, with glowing testimonials from clients worldwide.
Every engagement is built around three pillars that allow us to balance speed, diligence, and technical depth:
We begin by mapping the role to your threat landscape, infrastructure, and compliance needs. Then we activate our sourcing network to find candidates that others miss:
Cybersecurity hires must be both technically competent and trustworthy. Our multi-stage evaluation ensures both:
We balance urgency with diligence to deliver high-quality hires, fast:
We also use internal tooling to match roles with greater accuracy, so every recommendation is technically and culturally aligned.
Do you have IT recruitment needs?
Building a cybersecurity product is not the same as building a generic software platform; the engineering talent behind it needs to understand how vulnerabilities work, how detection systems are designed, and how performance failures translate into security gaps. Finding that kind of talent is a different challenge than standard technical hiring.
Mend.io, an Israeli leader in open-source security and software composition analysis (SCA), needed two senior hires to strengthen its vulnerability detection engine and scale performance-sensitive backend systems. The roles, a Senior Algorithmic Engineer and a Senior Go Developer, required deep expertise in graph theory, static analysis, distributed systems, and Go concurrency. These are not common skill combinations, and in the security product space, the candidate pool shrinks further.
DevsData LLC sourced across Eastern Europe, Israel, and selected EU markets, running scenario-based technical evaluations tailored to the product’s demands. The result: an average eight day time-to-offer, a 100% offer acceptance rate, and the majority of candidates sourced from passive talent pools unavailable through standard channels. Both engineers took ownership of core components quickly, improving algorithmic performance and backend throughput. The engagement shows how recruiting for security-critical products requires the same rigour and specialisation that pure cybersecurity hiring demands.
As cybersecurity threats become more common, harmful, and costly, security hiring cannot be overlooked. The stakes are great, and the margin of error is narrow. Building the ideal team is more than just filling seats; it is also about protecting data, maintaining compliance, retaining confidence, and keeping operations running.
However, due to talent scarcity, intense competition, and a shifting threat landscape, finding individuals with the right combination of technical expertise, problem-solving skills, and business understanding has become increasingly challenging. That is why a deliberate, forward-thinking recruitment strategy is required – clear role definitions, targeted outreach, thorough vetting, and competitive offers.
Partnering with a specialist like DevsData LLC gives you the edge. With extensive industry knowledge, a broad talent network, and a high-precision evaluation procedure, we reduce hiring time and risk and deliver cybersecurity specialists who make an immediate impact. In 2025 and beyond, resilience begins with the right people; let us ensure yours.
Frequently asked questions (FAQ)
DevsData – your premium technology partner
DevsData is a boutique tech recruitment and software agency. Develop your software project with veteran engineers or scale up an in-house tech team of developers with relevant industry experience.
Free consultation with a software expert
🎧 Schedule a meeting
FEATURED IN


DevsData LLC is truly exceptional – their backend developers are some of the best I’ve ever worked with.”

Nicholas Johnson
Mentor at YC, serial entrepreneur




Categories: Big data, data analytics | Software and technology | IT recruitment blog | IT in Poland | Content hub (blog)